Email authentication improves email deliverability. Using email authentication the conveyance and believability of your advertising emails by executing conventions that check your domain as the sender of your messages.

While email authentication doesn’t guarantee inbox placement, it significantly improves your chances. It acts as your first line of defense against spoofing, phishing, and spam-related issues that can damage your sender reputation.
In this blog, we focus on the three key email authentication protocols: SPF, DKIM, and DMARC. Each serves a different function, but all work together to protect recipient inboxes and ensure your emails come from a trusted source.
1. Sender Policy Framework (SPF)
SPF allows domain owners to specify which mail servers can send emails on their behalf. It helps receiving servers verify that incoming messages come from authorized sources, reducing the risk of forged emails and spam.
2. DomainKeys Identified Mail (DKIM)
DKIM confirms that an email’s content hasn’t been tampered with in transit by using cryptographic signatures. The sender’s server attaches a digital signature to each email, and the recipient’s server verifies it using the public key stored in DNS. If the keys match, the system recognizes the email as authentic.
How DKIM Works
If the content hasn’t been altered, the email passes DKIM verification.
DKIM authenticates email by allowing the sender to take responsibility for a message in a way the recipient can verify. It uses public key cryptography to confirm that an authorized mail server sent the message. This process helps detect forgery and prevents the delivery of harmful emails like spam.
- The sender’s Mail Transfer Agent (MTA) creates a signature based on the email content.
- The MTA adds the signature and sends the email.
- The recipient’s server fetches the sender’s public key from DNS and validates the signature.
3. DMARC (Domain-based Message Authentication, Reporting & Conformance)
DMARC builds on SPF and DKIM to give domain owners control over unauthenticated emails. It lets you instruct receiving servers on how to handle suspicious emails—whether to quarantine, reject, or report them. DMARC also provides insights into authentication performance and misuse.
Why SPF and DKIM Work Better Together
SPF and DKIM offer value individually, but when combined, they provide a more robust authentication framework. Together, they make it much harder for attackers to impersonate your domain and get past spam filters.
Authentication Strengthens Sending Reputation
ISPs and mailbox providers track domain reputation based on authentication. When you properly configure SPF, DKIM, and DMARC, ISPs recognize your domain as a trustworthy sender. A positive reputation improves your chances of landing in the inbox and accelerates how quickly receiving servers accept your mail.
Why Choose Gamalogic for Email Validation
Gamalogic offers one of the most accurate and cost-effective email validation solutions in the industry. Our real-time verification engine doesn’t rely on cached results—every check is live. We specialize in validating catch-all email addresses with a proprietary algorithm that sets us apart from the competition. Our service is lightning-fast, reliable, and priced at a fraction of the market standard.
An email professing to be from your bank or an organization you work with, yet it’s truly from another person. At that point you’ve seen direct that it is so natural to produce email. Authentication legitimates senders to demonstrate that their email isn’t produced and can help accepting servers like ISPs and corporate email servers control inbound spam.
Authentication and Sending Reputation
When you add authentication information to your domain, an additional advantage is that numerous ISPs use confirmation to follow sending notoriety. With authentication dealt with by your domain, notoriety with the accepting ISPs is impacted by your area and the emails sent for the benefit of your domain. This implies you keep up control over the emails that influence deliverability for your domain. Positive notoriety for your domain builds trust and improves deliverability, influencing whether your emails are gotten by spam blockers and how rapidly the getting servers will acknowledge mail from your domain.
Gamalogic email validation is one of the quick and robust services provided with the one-tenth price in the industry. We do not keep any cached data to resolve the old results. All data will be 100% real-time. Our unique algorithm will validate the catch-all addresses, this is our USP.
You might also like
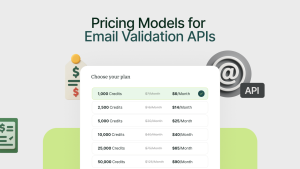
Pricing Models for Email Validation APIs: Cost per Check, Subscriptions and Hidden Costs
Discover how email validation API pricing works — from per-check costs to subscription models and hidden fees. Compare top providers and choose smartly.
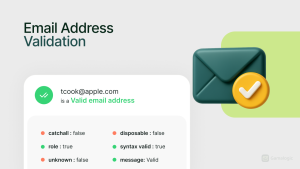
What is Email Validation? And How to Validate Email
Discover What is Email Validation , why it matters, and how third-party tools help improve deliverability, sender reputation, and ROI.

The Complete Guide to Email Validation APIs | Features, Benefits, How to integrate & Best Tools
Learn everything about The Complete Guide to Email Validation APIs ,their features, benefits, integration steps, and top tools to ensure accurate, secure, and deliverable email addresses for your business.






 No credit card required
No credit card required

Post your Comment.